In our previous article (SPIFFE Identity Federation: Extending Trust Across Boundaries), SPIFFE federation was examined as a mechanism for extending identity trust across independent trust domains. Bundles are exchanged, trust anchors are verified, and workloads authenticate each other using X.509 SVIDs over mTLS.
From a cryptographic standpoint, federation is elegant. Two workloads from different organizations can establish mutual trust without sharing a root CA. Identity is represented as a SPIFFE ID, and trust is derived from verified bundles. The protocol is minimal and precise.
At that level, federation is straightforward.
However, meaningful SPIFFE based communication in production environments requires more than bundle exchange and certificate validation. It requires a system in which identity, certificate lifecycle, and communication control remain coherent as complexity increases.
mTLS Is Only One Layer
For SPIFFE based mTLS communication to operate reliably, multiple layers must function together.
Workloads must be identified accurately. Certificates need to be issued, distributed, rotated, and eventually revoked. Workloads must be able to use those credentials without disruption during rotation. And there must be a clear, enforceable model that defines which identities are allowed to communicate.
Federation extends identity across trust domains. It does not eliminate the need to solve the other layers. When these responsibilities are handled by separate subsystems with different configuration models and runtime assumptions, operational complexity grows.
The friction usually appears not in cryptography, but in coordination.
Federation Expands the Identity Graph
Introducing federation expands the identity graph. External SVIDs are now present. Remote bundle endpoints are configured. Cross domain communication paths become possible.
The mechanics of verification remain consistent. The surface area that must be understood increases.
As trust domains multiply, so do the relationships between identities. Questions emerge that are less about certificate validity and more about system behavior. Which internal workloads can communicate with which external identities? How are those decisions enforced? Where is that enforcement happening?
Federation does not introduce these concerns. It amplifies their impact.
Fragmented Enforcement Increases Complexity
In many deployments, identity and enforcement are layered.
An identity system issues and rotates SVIDs. Another component terminates TLS. A separate policy engine evaluates authorization. Network rules may apply at IP. Observability is handled elsewhere.
Each layer may function correctly in isolation. The difficulty is that enforcement logic becomes distributed across boundaries that do not share the same identity model.
Identity is validated in one place. Authorization is decided in another. The actual network connection is controlled somewhere else. As more trust domains are introduced, the cost of aligning these layers increases.
The result is not necessarily misconfiguration. It is growing difficulty in reasoning about how identity translates into communication control.
Trust Scoping in Federation
Federation introduces a subtle but important boundary.
A federated trust domain should not implicitly become a generally trusted certificate authority within the environment. In Riptides, a federated bundle is associated explicitly with a declared SPIFFE trust domain and is used only to validate X.509 SVIDs that belong to that domain and conform to SPIFFE validation rules.
For example:
apiVersion: core.riptides.io/v1alpha1
kind: FederatedTrustDomain
metadata:
name: payments.acme.corp
spec:
trustDomain: payments.acme.corp
bundleEndpoint:
url: "https://payments.acme.corp/.well-known/spiffe-trust-domain-federation"
profile: HTTPS_WEB
caBundle: |
-----BEGIN CERTIFICATE-----
...
-----END CERTIFICATE-----The trustDomain defines the SPIFFE namespace being extended. The associated bundle endpoint is used exclusively for validating SVID chains that assert identities within that namespace. The CA material is not merged into a general purpose trust store, and it cannot validate unrelated TLS certificates.
This explicit scoping keeps trust boundaries clear as additional domains are federated.
Where the Assumption Breaks
In many service mesh deployments, the workload itself does not directly hold the SVID. The sidecar proxy terminates mTLS and presents the identity on behalf of the workload. From the remote service’s perspective, the connection originates from a verified SPIFFE ID associated with that proxy.
This abstraction simplifies application integration, but introduces a critical vulnerability: identity is attached to the proxy, not to the individual process that initiated the connection.
If a rogue or compromised process can route traffic through the proxy, it inherits the proxy’s valid identity. mTLS succeeds. Authorization policy evaluates the expected SPIFFE ID. The connection is allowed because the enforcement layer sees a legitimate identity.
Nothing is misconfigured. The system behaves exactly as designed.
The distinction is that identity validation and enforcement happen in user space at the proxy boundary, not at the point where a specific process creates a socket. The runtime origin of the connection is abstracted away.
When federation expands the set of reachable identities across trust domains, this becomes more consequential. A valid federated identity presented by the proxy is sufficient to authenticate externally, even if the initiating process was never intended to establish that relationship.
From Identity Validation to Runtime Enforcement
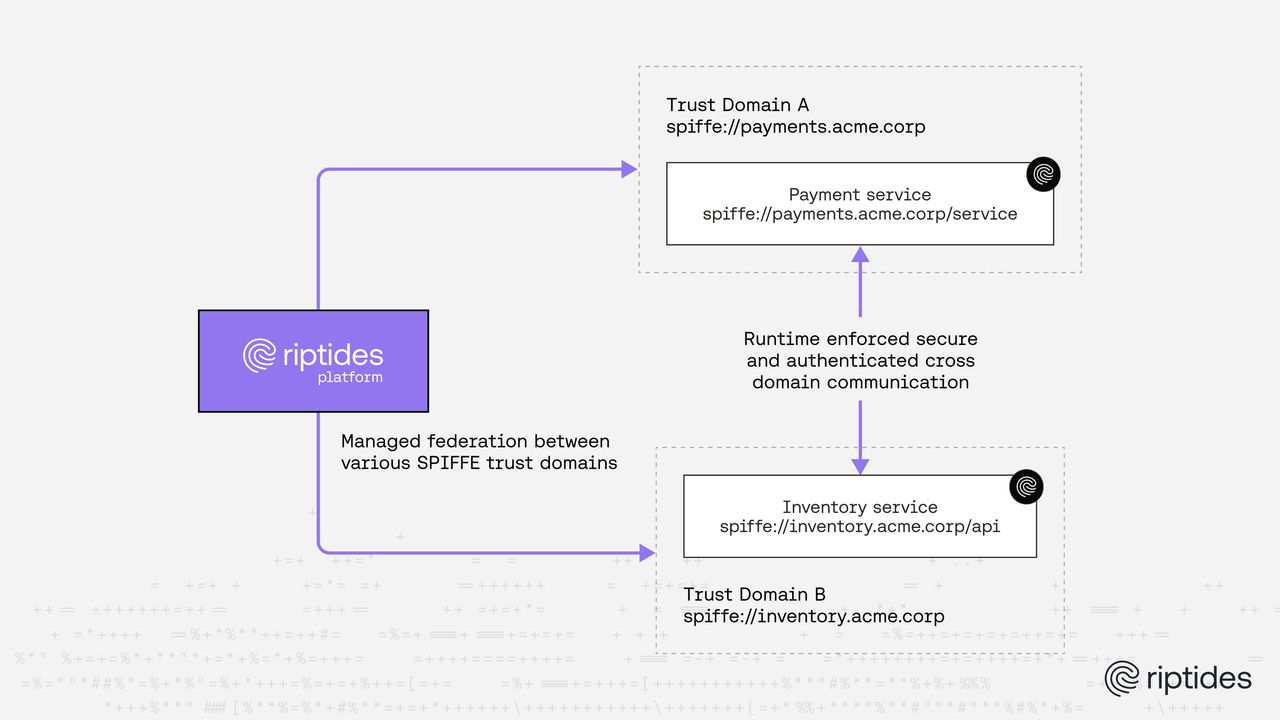
Riptides approaches workload identities and federation differently.
Once an SVID, local or federated, is validated against its corresponding trust domain bundle, the verified SPIFFE ID is bound directly to the originating process at socket communication time. Identity is attached at the connection boundary in the kernel rather than at a user space proxy.
Certificate distribution and rotation are handled transparently. Short lived credentials can rotate without application awareness. Revocation or bundle updates affect subsequent connection attempts immediately.
Communication policy is evaluated at the moment a connection is created. Enforcement happens before application logic or proxy layers interpret the traffic. A process cannot inherit identity simply by routing traffic through a shared proxy, because identity is bound to the runtime context of that process itself.
This alignment of identity validation, certificate lifecycle, and connection level enforcement reduces the number of independent subsystems that must agree for a policy decision to hold. Federation introduces additional identities into the model, but it does not introduce a new enforcement boundary or another user space layer.
Keeping the Model Coherent as Trust Expands
As additional trust domains are federated, the identity graph grows. In architectures where identity issuance, TLS termination, and policy enforcement are handled by distinct layers with separate control planes, each new trust relationship increases coordination overhead.
In a unified runtime model, federation extends the set of valid identities while enforcement remains centralized at the connection boundary. The same mechanism governs local and federated identities. The same policy model applies regardless of which trust domain issued the SVID.
The cryptographic mechanics of SPIFFE federation remain intentionally simple. The more complex challenge is maintaining a coherent operational model as trust relationships expand.
Federation determines which identities can authenticate across boundaries. Runtime enforcement determines which of those authenticated identities can actually communicate.
When these concerns are aligned, federation remains an extension of identity rather than an additional source of operational fragmentation.
If federation is already part of the architecture, it is worth examining where identity is actually bound and where enforcement truly happens. Riptides makes that boundary explicit at the runtime level. Explore the architecture or reach out if a deeper technical discussion would be useful.
If you enjoyed this post, follow us on LinkedIn and X for more updates. If you'd like to see Riptides in action, get in touch with us for a demo.